Cloud Services Press Release: Remain Informed on the most recent Advancements
Cloud Services Press Release: Remain Informed on the most recent Advancements
Blog Article
Boost Your Information Security With Reliable Cloud Storage Solutions
Enhancing information safety via dependable cloud storage space solutions is an essential element of modern company operations. Remain tuned to discover how cloud storage solutions can boost your data safety and security protocols and mitigate potential threats successfully.
Value of Data Security
The raising reliance on electronic platforms for storing and managing delicate info has actually made data safety and security more crucial than ever previously. Applying durable information security steps is important to securing versus potential threats.
Data protection assists stop unapproved accessibility, disclosure, change, or damage of data, making certain that it continues to be protected and shielded from malicious stars. By embracing best practices and leveraging sophisticated modern technologies, such as file encryption and accessibility controls, companies can improve their information protection pose and alleviate the likelihood of data violations.
Advantages of Cloud Storage
In today's data-driven landscape, cloud storage solutions use a wide variety of benefits that boost data protection and access for individuals and organizations alike. One key benefit of cloud storage space is its scalability. Customers can quickly readjust their storage requires, whether enhancing or lowering capacity, without the need for physical hardware upgrades. This versatility not just saves costs yet likewise makes certain that data storage lines up with current requirements.
An additional advantage is the improved information safety and security features given by credible cloud storage space companies. These services typically provide file encryption, data redundancy, and normal backups to safeguard information from violations, loss, or corruption.
Aspects for Selecting Supplier
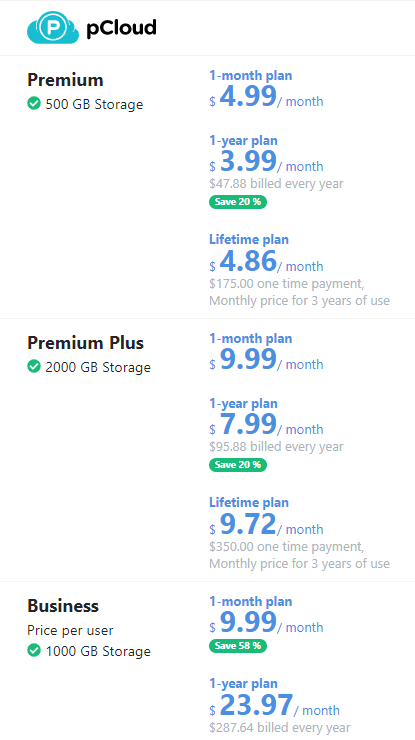
An additional vital factor is the level of information security and safety and security measures provided by the service provider. Make certain that the cloud storage service carries out robust security procedures to protect your information both in transit and at remainder. Scalability and adaptability are likewise key considerations when picking a provider. Your company's storage space needs might alter over time, so choose a copyright that can accommodate your developing needs without endangering data security. Evaluate the supplier's information back-up and catastrophe recovery abilities to ensure that your data stays obtainable and secured in the occasion of any type of unexpected cases.
Security and Information Protection
Making certain durable encryption protocols and stringent information protection measures is necessary when delegating delicate information to cloud storage solutions. File encryption plays an important role in safeguarding information both en route and at remainder within the cloud atmosphere. linkdaddy cloud services press release. By encrypting data, details is transformed right into a protected layout that can only be accessed with the proper decryption key. This assists protect against unauthorized accessibility to personal information, guaranteeing its discretion and integrity.
Security Best Practices
Implementing robust safety ideal techniques is paramount in protecting information integrity and privacy within cloud storage space solutions. In addition, normal security audits and vulnerability assessments are vital to recognize and fix any kind of possible weak points in the cloud storage space environment.
One more vital safety ideal method is information file encryption both in transportation and at remainder. published here Using file encryption procedures guarantees that data remains protected even if intercepted during transmission or storage. It is additionally advisable to apply automatic back-up and catastrophe healing treatments to secure against data loss as a result of unforeseen events like cyberattacks or system failures.
Furthermore, keeping updated safety and security patches and remaining notified about the most recent protection dangers and trends are crucial for aggressive protection administration. Education and learning and training for workers on safety and security protocols and ideal methods additionally play a crucial role in strengthening the overall protection pose of cloud storage space solutions. By sticking to these protection finest techniques, organizations can boost the protection of their delicate data kept in the cloud.
Final Thought
Finally, reliable cloud storage space solutions supply a effective and protected solution for protecting your information. With sophisticated file encryption, data redundancy, and normal back-ups, these services ensure the confidentiality, integrity, and schedule of your details. By very carefully adhering to and choosing a trusted provider protection finest practices, you can improve your general data safety position and guard your useful data official statement from prospective cyber threats.
Information safety and security aids avoid unapproved access, disclosure, change, or destruction of information, guaranteeing that it continues to be protected and shielded from harmful stars. By adopting finest practices and leveraging sophisticated modern technologies, such as encryption and gain access to controls, organizations can improve their information security pose and mitigate the probability of information breaches. These services commonly provide security, information redundancy, and regular backups to shield data from breaches, loss, or corruption - linkdaddy cloud services. Assess the copyright's data backup and calamity recovery capabilities to make sure that your information continues to be accessible and safeguarded in the event of any kind of unpredicted incidents
By thoroughly adhering to and selecting a trusted supplier protection ideal techniques, you can boost your total information safety pose and guard your beneficial information from prospective cyber dangers.
Report this page